In today's digital landscape, integrating security into the software development process isn't just a best practice; it's imperative. Given universal accessibility, adopting a security-focused SDLC is crucial to preemptively address potential vulnerabilities. Tools like application security posture management provide comprehensive insights, bolstering protective measures against cyber threats. Proactively integrating security measures from inception mitigates risks and protects both software and users.
Implementing Secure SDLC offers numerous benefits. It aids in early risk detection and mitigation, reduces post-deployment fix expenses, and fosters user trust through secure product delivery. Proper implementation allows teams to plan releases efficiently, identifying and resolving issues preemptively to safeguard schedules. With Secure SDLC, security efforts are developer-driven, ensuring expertise-driven issue resolution. Early issue addressing minimizes total ownership costs, preventing substantial cost escalations in later stages.
Building Security from the Ground Up
Secure SDLC consists of critical steps, all essential for software security. Omittingany part compromises overall security. Full implementation ensures product security.
Contact Us For Customized SDLC GuidanceAnalyzing Requirements
This initial phase involves identifying and defining security requirements. It sets the stage for the rest of the development process, ensuring that security considerations are embedded from the start.
Business Requirement
Security Consideration
Checking System Design
At this stage, the focus is on ensuring that the system's architecture incorporatesthe necessary security measures. It involves evaluating the design to identify any potential security vulnerabilities.
Design Requirement
Security Consideration
Strengthening the Core
This phase integrates security practices into the actual coding and development process. It includes adopting secure coding practices and ensuring that security is a consideration throughout the development.
We also need to note that modern application developers need to consider more than just their own code, as most contemporary applications are not built entirely from scratch. They often utilize pre-existing functionalities, primarily sourced from free open-source components, to rapidly deliver new features and value to their organizations. In fact, over 90% of modern applications deployed are composed of these open-source elements. Software Composition Analysis (SCA) tools are typically employed to examine these components.
Verification
Verification involves rigorous security testing and reviews. This step is crucial to identify and address any security issues before the software's deployment. Its highly recommended during this step to enhancing CI/CD process and include different security checks and using static code analyzers to find potential vulnerabilities.
Maintenance and Evolution
Post-release, vulnerabilities, initially overlooked in development, may emerge. These flaws, originating from code or open-source components, increase "zero-day" risks. Remediation typically falls to developers, potentially requiring significant rewrites. External sources like ethical hackers or bug bounty programs may also identify issues. Proactive planning and solutions in subsequent releases are vital for ongoing security.
Best Practices in Secure SDLC
Secure SDLC success varies with the development team's abilities and needs, making a one-size-fits-all approach impractical. It involves method changes, new tools, and a cultural shift, unique to each organization.
Contact Us For Customized SDLC GuidanceHow we can assist you
Explore personalized support options designed for a smooth and enjoyable experience with us.

Development Stages
Navigate through our developmental stages, tracing the journey from concept to fruition.
Learn More Development Stages
Our Process
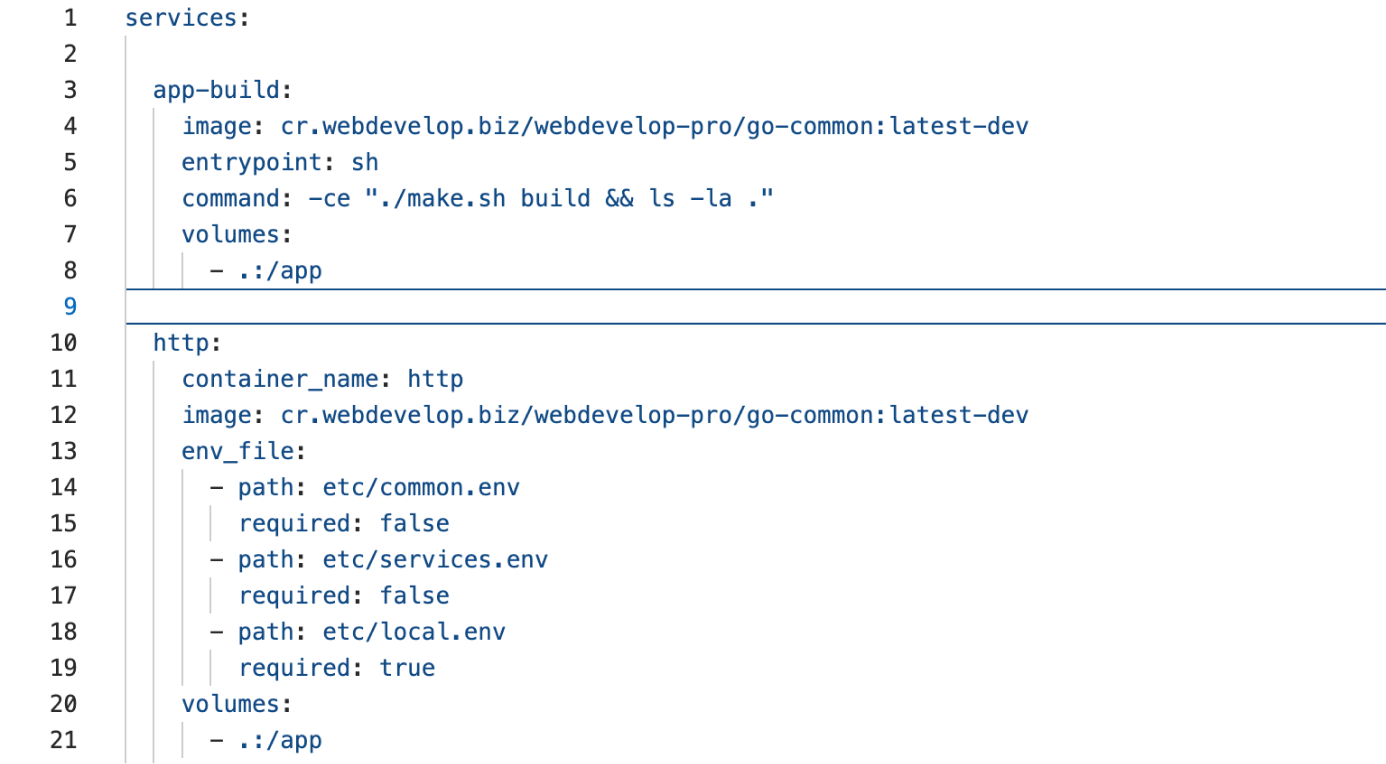
Explore our pipelines, revealing diverse pathways shaping our future offerings.
Learn More Our Process